Malware Filter Modes
What is the Malware Filter?
The Malware Filter blocks known (and unknown) malicious domains that can distribute malware, operate botnet C&C servers, or can cause harm you the end user. There are several modes that this Filter can be operated in, which leverages different types of datasets as well as machine learning.
Modes of Operation
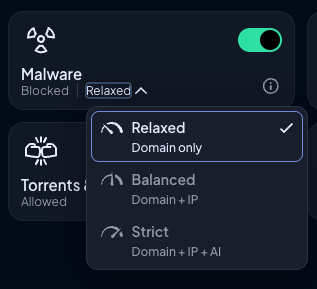
The Malware filter blocks domains that can harm your device or network. There are three modes to choose from.
Relaxed
Blocks malicious domain names that appear in dozens of threat intelligence feeds we subscribe to. This filter only references domain name feeds, and is updated multiple times each hour.
Balanced
Includes everything that the Relaxed Filter does, but also blocks domain names that resolve to malicious IP addresses from dozens of IP threat intelligence feeds. This mode will prevent domains from loading simply because they resolve to IPs that belong to malicious or high risk networks and hosting providers. Control D is the only DNS service that has this feature.
Strict
Includes everything that the Balanced Filter does, but also enables machine learning assisted malware detection that blocks domains based 30+ signals and does not reference any threat intel feeds (although it was trained on those feeds).
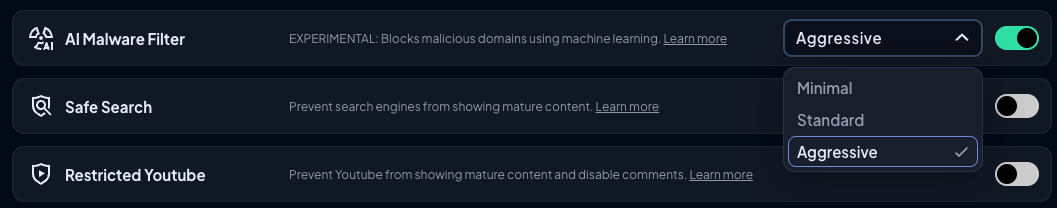
This mode can catch things before they're even detected by traditional threat intel feeds. There are 3 sub-levels of strictness ("AI Strength"), which can be configured in Profile Options. The more strict it is, the higher chance of it catching and blocking a malicious domain, but so is the chance of a false positive.
Learn more about the ML Malware Filter.
Recommended Settings
We recommend running the Malware Filter in Strict mode, and the AI Malware Filter in Minimal Mode. This has the lowest chance of false positives, however if you prefer it to be more aggressive feel free to increase the level.
Updated 7 months ago